Cloudflare integration
You can set up VerifiedVisitors for Cloudflare using our Worker module.
The Worker executes on each request on a proxied route, calls the VerifiedVisitors API for an access control decision, and serves a mitigation or allows the request through.
This module injects a JS agent into HTML responses, which displays challenge pages and collects information about the visitor's browser to improve threat detection and visitor categorisation.
- Domains you wish to protect must be proxied behind Cloudflare.
- Domains you wish to protect must not have an existing worker route configured.
- You must have a Worker plan suitable for your account-wide request rate if it is at or over 100,000 per day.
This integration can be configured automatically from VerifiedVisitors, which manages the worker module and route setup when provided with a Cloudflare API token.
The worker can also be installed manually by deploying the implementation manually.
Cloudflare worker limits
The worker creates a subrequest for every visitor request, therefore it's usage will be in line with your web traffic.
Because of this, the implementation is subject to the limitations of your Cloudflare Worker Plan. If you have over 100,000 requests per day, or burst traffic that exceeds 1,000 requests per minute, you must upgrade to a suitable plan to support both the VerifiedVisitors service and any existing worker implementations you may have.
In some cases, the worker may still trigger Cloudflare's internal anti-abuse protections in periods of high load due to the number of subrequests to VerifiedVisitors from the worker. Throttled requests should be visible when reviewing your Cloudflare firewall events.
This can be easily resolved by contacting Cloudflare support asking them to
disable the rate limit for all requests to api.verifiedvisitors.com.
Setup
Configuring the worker via VerifiedVisitors takes care of the process of configuring worker scripts and routes for you.
To do this, VerifiedVisitors integrates with the Cloudflare API to manage worker resources, and requires access using a limited API token.
1. Create an API token in your Cloudflare account
Login to your Cloudflare account and create a new API token from the profile API tokens page.
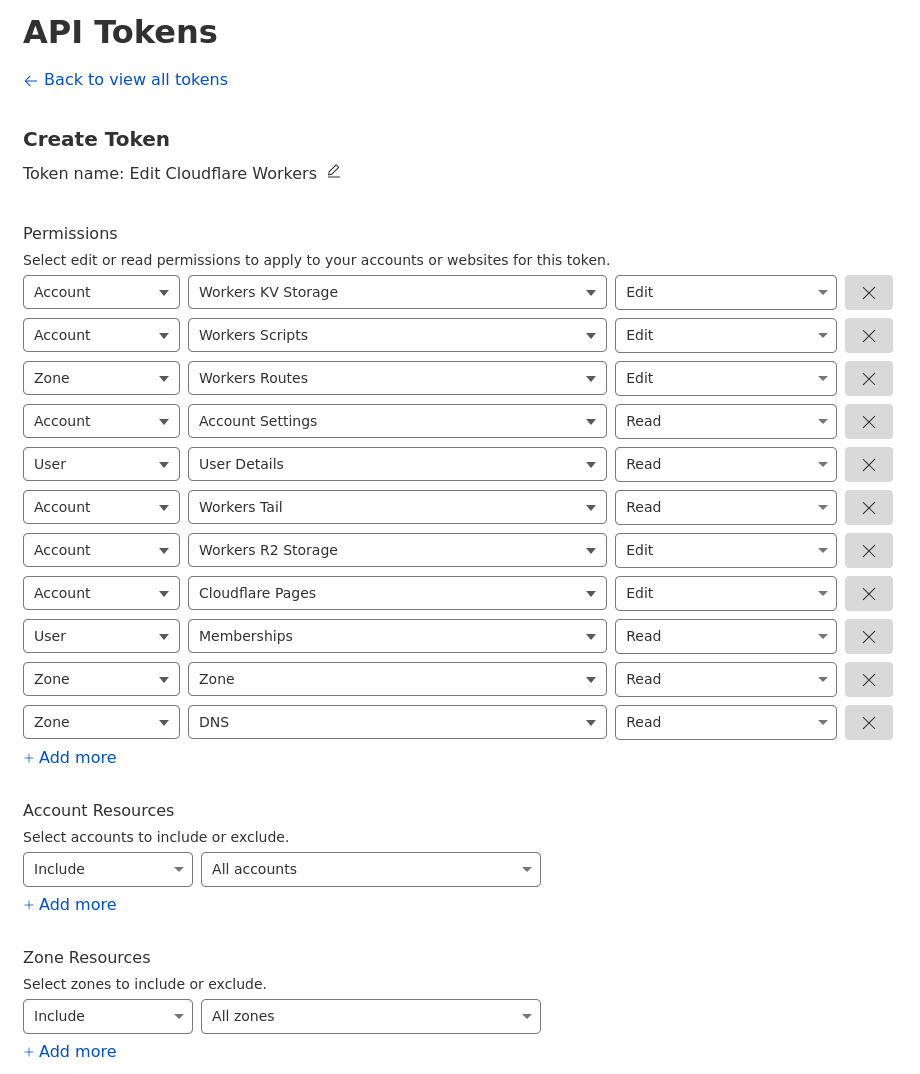
On the next screen, choose the "Edit Cloudflare Workers" token template.

On the next screen you will be prompted to alter the token's permissions.
Give the token a descriptive name and add the following permissions:
- zone: zone (read)
- zone: DNS (read)
You may optionally further restrict the token to specific accounts or zones from this screen or specify "all accounts" and "all zones".
Create the token by clicking "continue to summary", then "create token".
Keep a note of the token displayed for the next step.
If for any reason you need to roll (invalidate) the token, you must re-configure the token as detailed in the next step.
Invalidating a token does not affect sites that have already been configured in VerifiedVisitors, but will prevent automatic worker management.
2. Configure the token in VerifiedVisitors
Login to your VerifiedVisitors account go to the Connect Cloudflare page.
Select the appropriate authentication type and enter the API token you created in step 1, and click submit.
If successful, we will have now integrated with your Cloudflare account, allowing you to manage your integration from within VerifiedVisitors.
API tokens are secured with column-level encryption in addition to the in-transit and at-rest encryption that is applied to all data.
3. Add sites to be protected
In VerifiedVisitors, go to the add site page and select "Cloudflare" as the integration.
In the next screen you will be prompted with a list of Cloudflare zones and their (sub)domains that can be protected.
To add a site, select the zone and any (sub)domains using the dropdown, and click "add sites".
VerifiedVisitors will automatically upload the worker script to Cloudflare and configure the worker routes.